Digital identity
made simple
Create trust at onboarding and beyond with a complete, AI-powered digital identity solution built to help you know your customers online. Automation allows you to acquire new customers and reduce costs while meeting global KYC and AML compliance.
Digital identity
made simple
Create trust at onboarding and beyond with a complete, AI-powered digital identity solution built to help you know your customers online. Automation allows you to acquire new customers and reduce costs while meeting global KYC and AML compliance.
How can Onfido
help your business?
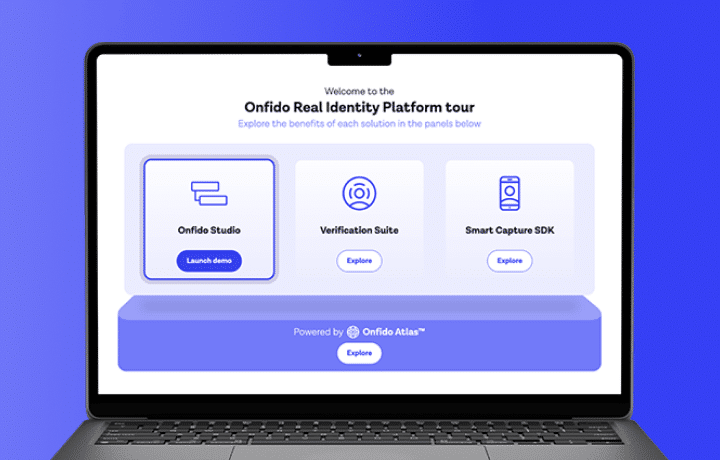
The Real Identity Platform
Put digital trust at the core of every customer interaction. Powered by fast, fair, and accurate AI, the Real Identity Platform brings together a global suite of identity verifications and signals into an easy-to-use orchestration studio.
Real Identity Platform tour
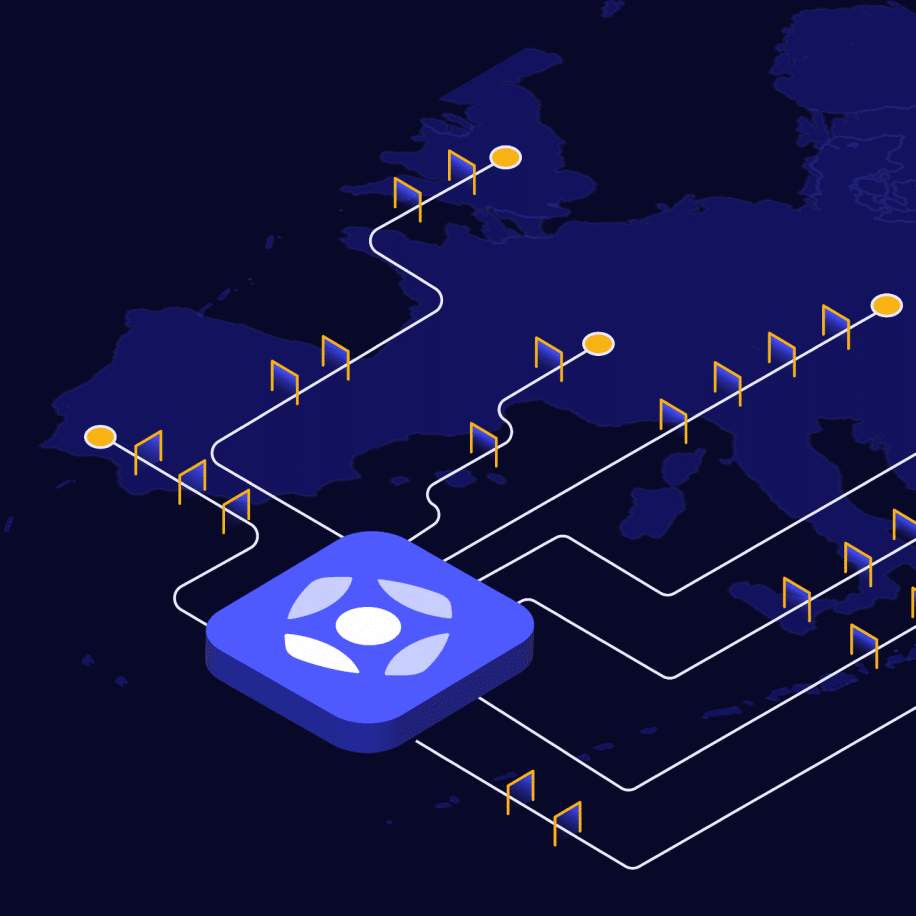
Flexible compliance package
Meet complex local regulatory needs and remotely onboard customers across Europe with an off-the-shelf compliance solution. Onfido’s Compliance Suite combines ETSI-certified identity verification with Qualified Electronic Signature (QES) and One-time Password (OTP) to offer simple, seamless, and eIDAS-compliant onboarding.
Built by developers for developers
Developer Hub
Get everything you need to configure and integrate with the Onfido Real Identity Platform.
API reference
Make integration quick and efficient using our comprehensive technical reference guides.
Professional Services
Our integration and success teams’ mission is to deliver maximum value for our customer.
Recognized as a leader
With more than a decade of identity verification, fraud detection, and AI development experience, Onfido is recognized as a global technology leader providing automated digital identity and authentication solutions.